
A container-based approach to boot a full Android system on regular GNU/Linux systems running Wayland based desktop environments.



A container-based approach to boot a full Android system on regular GNU/Linux systems running Wayland based desktop environments.


: Clearly define data ownership and review Service Level Agreements (SLAs) with your Cloud Service Provider (CSP).
: Map security goals to growth and stability targets to ensure executive support.
: Use tools like the Microsoft Defender for Cloud dashboard to track compliance against industry benchmarks. 2. Map the Attack Surface You cannot secure what you cannot see. Cloud Security Strategy: 5 Steps to Build a Secure Plan
Before implementing tools, understand your business context and the legal landscape of your data.
Developing a cloud security plan requires a blend of strategic governance and technical controls. While "AZMATH" does not correspond to a standard industry framework, effective planning typically follows a structured path of visibility, protection, and continuous improvement. 1. Assess and Align Goals
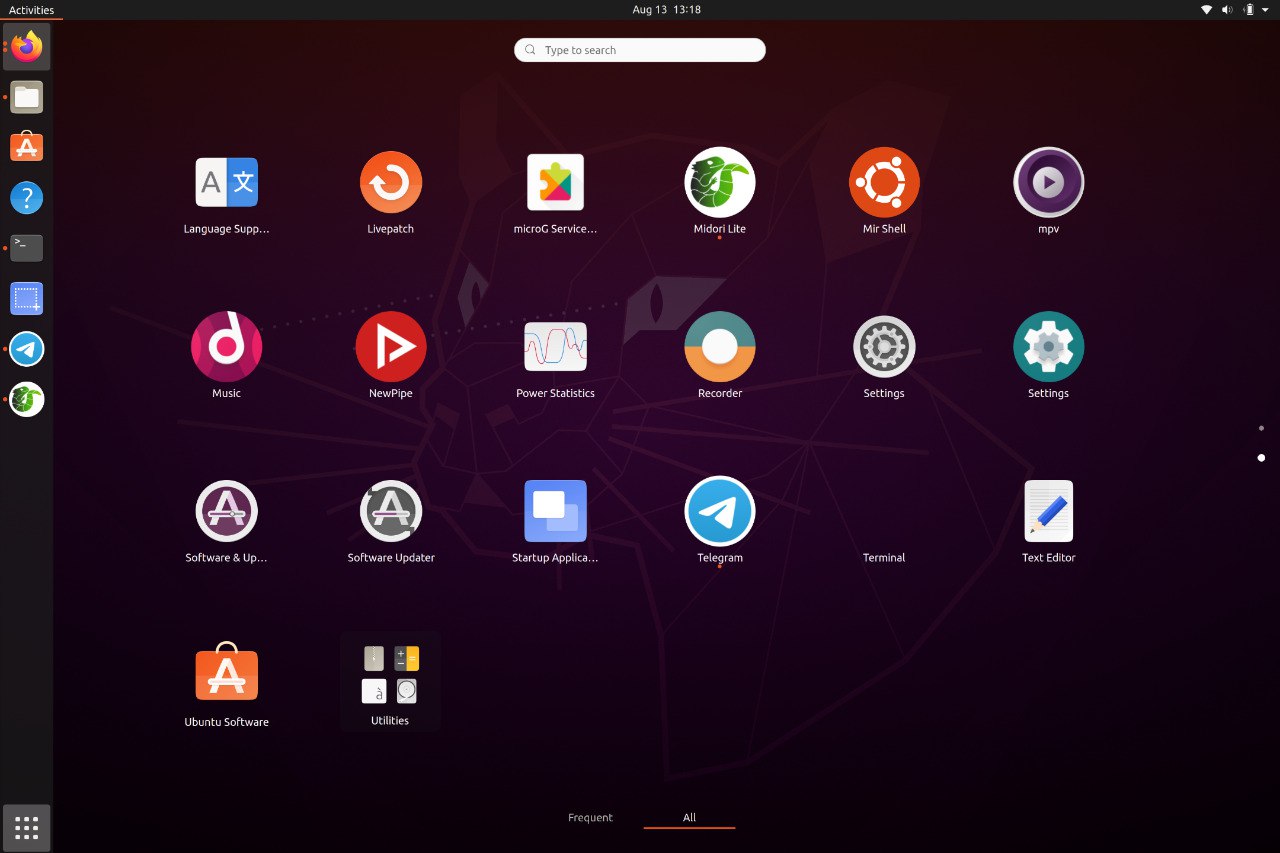
Waydroid brings all the apps you love, right to your desktop, working side by side your Linux applications.
The Android inside the container has direct access to needed hardwares.
The Android runtime environment ships with a minimal customized Android system image based on LineageOS. The used image is currently based on Android 13
Our documentation site can be found at docs.waydro.id
Bug Reports can be filed on our repo Github Repo
Our development repositories are hosted on Github
Please refer to our installation docs for complete installation guide.
You can also manually download our images from
 SourceForge
SourceForge

For systemd distributions
Follow the install instructions for your linux distribution. You can find a list in our docs.
After installing you should start the waydroid-container service, if it was not started automatically:
sudo systemctl enable --now waydroid-container
Then launch Waydroid from the applications menu and follow the first-launch wizard.
If prompted, use the following links for System OTA and Vendor OTA:
https://ota.waydro.id/system
https://ota.waydro.id/vendor
For further instructions, please visit the docs site here
: Clearly define data ownership and review Service Level Agreements (SLAs) with your Cloud Service Provider (CSP).
: Map security goals to growth and stability targets to ensure executive support.
: Use tools like the Microsoft Defender for Cloud dashboard to track compliance against industry benchmarks. 2. Map the Attack Surface You cannot secure what you cannot see. Cloud Security Strategy: 5 Steps to Build a Secure Plan
Before implementing tools, understand your business context and the legal landscape of your data.
Developing a cloud security plan requires a blend of strategic governance and technical controls. While "AZMATH" does not correspond to a standard industry framework, effective planning typically follows a structured path of visibility, protection, and continuous improvement. 1. Assess and Align Goals
Here are the members of our team







