Related posts
Marc-Andre ChartrandMarch 05 20263 Min Read
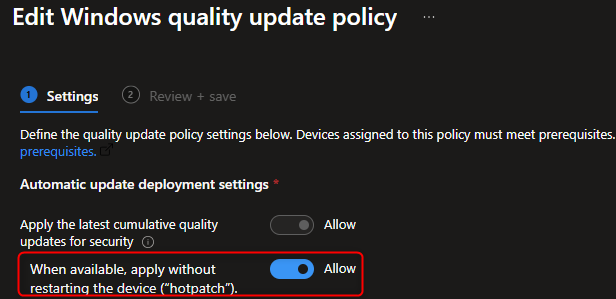
How to Configure Windows Hotpatch with Intune
Microsoft has introduced Hotpatch for Windows 11 Enterprise, a feature that allows you to apply...

Jonathan LefebvreNovember 14 20259 Min Read
Step-by-Step SCCM 2509 Upgrade Guide
Microsoft has released the second SCCM version for 2025, as the release cadence is now reduced to...
Jonathan LefebvreSeptember 08 20257 Min Read
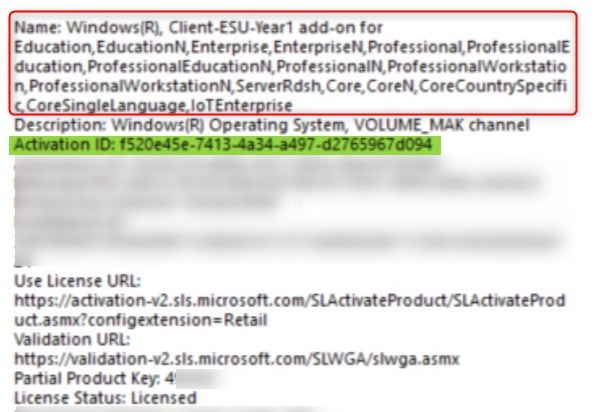
Deploy Windows 10 Extended security update key (ESU) with Intune or SCCM
With Windows 10 support ending October 14, 2025, organizations face a critical choice: upgrade to...



: Generates and compares MD5/SHA-256 hashes to ensure the file was not corrupted or altered during transit.
This feature allows you to preview and validate the contents of an archive like 23734.rar without actually extracting files to your primary system.
: If the archive contains a mix of documents, images, and executables, the utility automatically sorts them into temporary workspace folders for easier review.
: Automatically runs the archive’s contents through a multi-engine malware check before any files are touched by your operating system.
If you received this file from an unsolicited source or a suspicious email, do not open it. Encrypted or strangely named .rar files are common vectors for malware.
: Once the files are verified as safe, you can extract them directly to a specific "Project" folder named after the archive (e.g., /Downloads/Project_23734/ ).
: Instantly view the internal folder structure and file metadata (size, creation date, and extensions) within an isolated environment.
Because the contents of the file are unknown, I have generated a for a hypothetical Secure Archive Management Utility . This feature is designed to help you safely interact with unknown .rar files by prioritizing security and organization. Feature: "Sandboxed Content Inspector"